Rekeying: The Hidden Cost of Grocery Store Turnover
Rekeying: The Hidden Cost of Grocery Store Turnover
Read More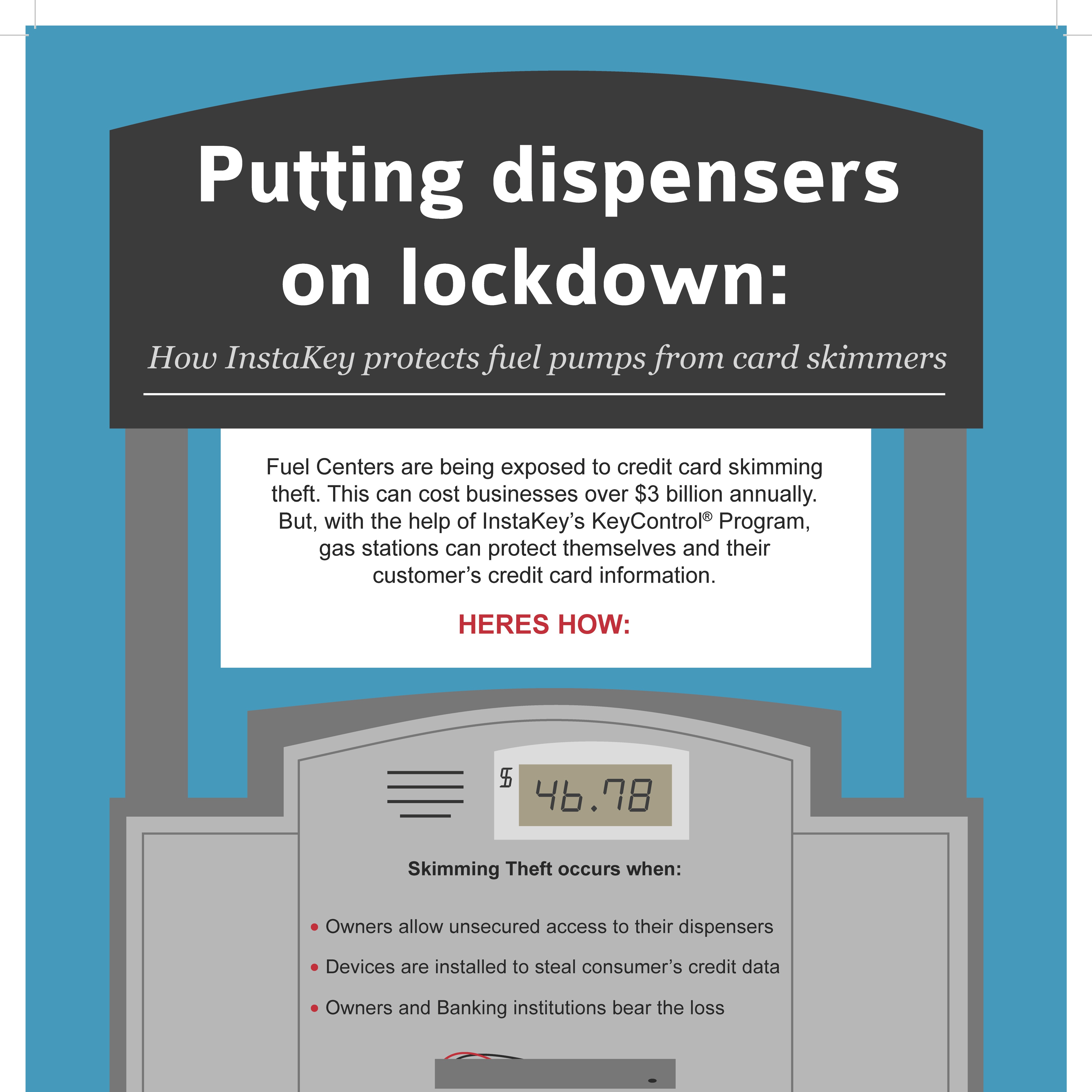 Download Infographic
Download InfographicAs more motorists use debit and credit cards to pay for their fuel purchases at gas stations, these establishments have become more susceptible to a new and growing threat: card skimmers. While these devices have been around for several years now, criminals are constantly improving their techniques to capture the sensitive data contained on consumers’ debit and credit cards. According to Bank Info Security, this process of secretly skimming payment cards from unsuspecting customers is estimated to be a $8 billion-a-year crime in the U.S., costing businesses $3 billion and banks $5 billion.
When owners allow uncontrolled access to their fuel dispensers, criminals can place a device over the mouth of a card reader. This device, called the skimmer, looks like a normal card slot, so the majority of customers are unaware of any threat. Often these skimmers will contain diagrams showing the proper way to use the card and Braille instructions, which add to the illusion of authenticity. Since nothing looks amiss, customers slide their card through the fake reader as they would normally, and this device captures the sensitive financial data contained on the debit and credit cards.
In other methods, a criminal will place a PIN-capture overlay device on top of the legitimate PIN entry pad. This helps capture the customer’s PIN as well as the information already contained on the card. Other methods include placing a hidden camera close to the skimmer so the criminal can see the number pushed to activate a customer’s PIN.
These techniques allow criminals to clone the debit or credit card and, armed with the PIN, these scammers can then use the data to steal the victim’s identity and rack up the charges on these unsuspecting individuals.
In many cases, these credit cards are used to purchase gas where they then siphon fuel into large tanks, reported The Wall Street Journal.
According to another article published by The Journal, businesses must update their checkout systems before Oct. 1, 2015. If an establishment fails to comply with the new standard, it will be liable for losses if counterfeit cards are used.
While the victim is the one who gets the fraudulent activity charged to his or her accounts, it’s actually the gas stations and banks who end up footing the bills.
In addition, these illegal activities undermine the integrity of the point-of-sale system, thereby spreading mistrust among consumers and stores alike, The PCI Security Standards Council reported.
Despite the growing presence of these illegal factors, there are fortunately ways gas station owners can protect their businesses against this thievery.
Skimmers gain access to the sensitive financial data by stealing or copying universal keys that they then use to open up point-of-sale terminals of the fuel pumps to install the device. However, InstaKey Fuel Center Clients are not limited to using these universal keys that work for all fuel pumps. Instead, these clients obtain custom keys that are restricted to work only at authorized locations and in pre-approved locks. This significantly decreases the chances of a skimmer gaining access to the fuel pumps.
These keys contain a unique serial number that cannot be copied and cloned on a mass market blank key. In addition, gas station owners can track and monitor these keys using cloud-based software, providing them with a constant, real-time ability to account for the keys at any given moment.
In the event that a skimmer does gain access to a fuel pump master key, it is extremely expensive and time consuming for owners to go around and replace the locks on all the fuel pump units. This process not only drains precious resources, it also leaves the pumps vulnerable in the interim before the keys are replaced. However, when utilizing rekeyable locks, owners quickly and easily reset the lock with the turn of a key. This ability to reset locks without replacing any of the hardware provides an additional layer of security and dramatically reduces the risk of a security breach.
Rekeying: The Hidden Cost of Grocery Store Turnover
Read MoreHOW MUCH ARE YOU SPENDING TO REKEY YOUR RESTAURANT LOCATIONS YEARLY? Learn how rekeying costs compare for traditional ...
Read More{Inforgraphic} Turnover and costs of rekeying in the retail industry for 2022. Learn more about cost reduction aspects ...
Read More