Key Management Made Simple - No Matter What Type of Keys
Keeping control of keys and key holders requires an organized system of documentation. But how can pieces of brass be ...
Read More
Sometimes the most effective security protocols are the simplest and most straightforward. And while many of them might seem like common sense in hindsight, they can often be overlooked or forgotten in the midst of a busy, demanding workplace that pushes and pulls managers in countless directions throughout the day. Still, something as obvious as remembering to collect keys when an employee leaves the organization can keep your facilities and workforce safe and secure, eliminating the need for time-consuming and costly rekeying – as long as you’re using a serialized, restricted key system. At InstaKey, we specialize in providing you such solutions for lasting security and cost efficiency.
While management may or may not devote much time and effort into a basic concept like keys, the different types of keying systems can actually have a significant impact on security, budget and overall company efficiency. If an organization utilizes a traditional mechanical key system for the entry points within their facility, they will continually be exposed to security risks, whether or not they collect keys from an employee exiting the company. Since these types of keying systems use relatively generic key blank, they can easily be reproduced by a locksmith or even a hardware store. As most managers are already aware, the simple act of stamping anti-reproduction verbiage on a set of keys has little, if any, effect on an individual’s ability to make copies.
Obviously, using such a system creates and maintains a constant risk exposure for businesses because they have no ability to prevent copies of keys being made. In such a system, even when keys are collected from the exiting employee, management still must rekey the facilities in case other unauthorized copies exist. If they do not, all workers, equipment and potentially sensitive materials are at risk. Also, given the typically exorbitant cost associated with rekeying facility doors, this can represent a significant ongoing cost to the employer, especially if the business experiences significant turnover in their workforce.
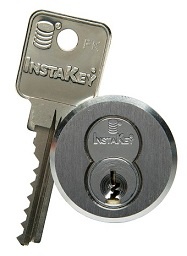
Using a serialized restricted key system avoids these costs and a risk exposure but eliminates an employee’s ability to make copies of their keys. Locksmiths and hardware stores do not have access to the key blanks used with these proprietary systems. Furthermore, since a serialized key system assigns a unique serial number to every key in use throughout the workforce, simply matching those serial numbers to those on the keys returned by an exiting employee can ensure continued company security.
Once again, a few simple and straightforward key procedures can make management’s life much easier while minimizing excessive costs and risk exposure. For instance, employees might not put much importance on their issued work keys, but management can integrate policies that create that needed importance. If a fine is levied upon an exiting employee when they fail to return their issued set of keys, they will value those keys significantly more than they would have otherwise. If the employees are contractually obligated to return their keys, the thought of being legally bound to care for and promptly return them upon exiting the company will create a sense of urgency around those keys.
Furthermore, maintaining a thorough receipt log for all issued keys will ensure the system is current, efficient and well-organized, making it easy for management to continually track which employees have particular keys. When an employee leaves the organization, the receipt log provides immediate information regarding the specific keys the worker is responsible for returning to the company. Utilizing a cloud-based receipt system maximizes the efficiency, immediacy and availability of such information, further enhancing a company’s overall security and productivity. A cloud-based system is also extraordinarily useful in providing insight into the overall health of your key control program and can readily identify any possible systemic issues that need to be resolved.
Aside from security, one of the biggest impacts a key control program has is on the budget. When a company uses a traditional mechanical key system, it not only continues to expose its workforce and facilities to risk, it also creates a significant ongoing cost. Rekeying even a portion of a facility can be extremely expensive and draining on a budget, possibly affecting overall company productivity.
However, when an organization uses InstaKey’s KeyControl® Program, these excessive ongoing costs are eliminated by removing an employee’s ability to reproduce keys. Simply put, solutions from InstaKey can be a tremendous cost-cutter to an organization’s budget while also significantly enhancing overall safety and security for all employees and facilities.

When working with InstaKey, you have a partner in KeyControl® that will help you manage keys and key holders, ensuring security for facilities and savings for you. With our innovative restricted key solutions, we remove those costly risk exposures to lost or stolen keys that can possibly be reproduced. Not only are these solutions significantly more budget-friendly than rekeying facilities but, more importantly, they provide lasting safety and security for the entire organization.
We take our partnerships seriously. With a decades-long track record of providing an unparalleled level of professionalism and expertise in KeyControl® for hundreds of organizations, we can help you find a solution that suits your company’s specific needs. Between restricted key programs, cloud-based management solutions and exemplary customer service, InstaKey is a partner to trust when integrating a key control program into your business.
Keeping control of keys and key holders requires an organized system of documentation. But how can pieces of brass be ...
Read MoreRestricted keys or non-restricted. That is the question. Learn which company keys to choose and an IC Cores spoiler. ...
Read MoreUsing restricted keys and key tracking together creates a strong foundation for you to build your physical security. ...
Read More