Master Key System Best Practices
As a business owner or manager in charge of security, having complete access to all entry points is expected. A master key system provides tiered access to locks across your organization. While a master key system provides you and other authorized personnel with necessary access across all entry points, it can also create a security risk if not properly implemented. Your master keys should be limited only to the people who need them, should not be duplicable, and should conform to other secure key control practices, like serial numbering, user-rekeyable locks, and key tracking. Let’s dive into the best practices to put in place with your master key system.
Limit Master Key Holders
A good best practice across all key systems is to limit the number of people who have keys to only those who need individual access to certain entry points. When talking about master key holders, it’s even more important to limit your master keys to only the people who need to have high-level access. As you create your master key system, consider how you can limit master key holders to only necessary individuals, while providing more specific and restricted access to other key holders.
When designing your master key system, consider how you can group access to single locations, similar entry points, or by other organizational groups to limit the cases of a single master key having total access across your organization. While carrying multiple keys can be a hassle, dealing with a lost master key that has access to a few locations rather than a master key that has access to every location in your organization can make a big difference in the time, money, and stress of rekeying.
Prepare for a Lost Master Key
Losing or misplacing a master key is a big security risk that has to be quickly addressed to avoid a keyed security breach. With a lost or misplaced master key, the need for a quick, efficient response is even more vital, as you’ll need to change the locks across every point of entry associated with that master key, which can be an entire organization or multiple locations – and you can be sure this will come with a huge price tag.
To alleviate the major cost of rekeying after a master key is lost, the best practice is to install user-rekeyable locks. InstaKey’s innovative rekeyable locks don’t have to be removed from the lock hardware to be changed and can be rekeyed with a special key which is inserted into each affected lock and turned 180 degrees. With a simple key turn, your locks have been rekeyed and new keys can be distributed to affected key holders. Rekeyable locks can also make complicated rekeys easy (and cheaper) with lock changes independent of each level (master, sub-master, grand master, etc.). If a master key is lost, only locks on the master level need to be rekeyed. All other levels of the key system go unaffected.
Restricted Master Key System
A crucial component of a secure master key system is using keys that can’t be duplicated without authorization. Restricted key blanks are not available on the open market, so if your master keys are restricted, they can’t be copied by a local hardware store or locksmith and can only be duplicated with authorization given to your key provider. When you use keys that are not restricted, you are opening up your organization to security threats and have little control over mitigating those threats.
Using restricted keys eliminates the possibility of unauthorized key duplicates. Not only does this improve your security and peace of mind for all key holders across your organization, it’s a necessary practice for master key system security. Serialized, or keys with other unique identifiers, make key tracking easier because each key is now individualized. Not unlike your social security number, giving an identifier to a key gives them a name and makes them trackable and easy to associate with people and points of entry.
Key Identification
Adopting a master key system will surely cut down on the number of keys carried by key holders. But sometimes multiple keys are still carried. For individuals with multiple keys, keeping track of which key opens which door can save the time and hassle of having to try each one in the lock, but key labels can be a dangerous security risk if they aren’t coded. The worst practice you or your employees could put in place is labeling each key with the access point it opens. If that key is ever lost, someone could know exactly what door that key opens and undermine your security.
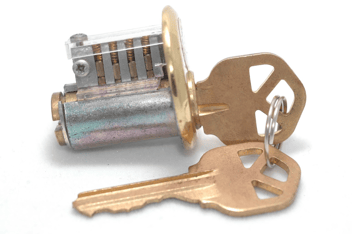
Keeping track of multiple keys in a master key system becomes simpler by using the Door Hardware Institute’s (DHI) Keying Standards. A DHI abbreviation is the nomenclature used for how the cylinder is pinned to match with the key bitting or cuts, so the key rotates in the cylinder. This DHI abbreviation stamped on your key lets you know the key series that you are using. For example, an FA series Master key will operate any FA series cylinders. Each key uses a specific abbreviation stamp to make it easier to know what it opens. That way you don’t have to remember which key unlocks what. It should also be noted that InstaKey uses these industry standards for corporate master key design to keep everything organized such as chart accuracy, cylinder installations, and keys assigned to the right people for you.
Of course, you could also keep it simple with color coding keys with key fobs or tags if you don’t have a DHI stamped on the key.
Master Key Control
Keeping track of who has which keys is a crucial part of your key control, but it’s especially important for master keys. Knowing who has each key, what doors it opens, and other key control data is needed to maintain security, perform efficient audits, change key access with employee turnover and manage costs.
Audit Your Keys Regularly
By performing regular key audits, you can keep a careful eye on who has which keys, which is especially important for master keys. If you have multiple master key holders, or different levels of master keys (including sub-masters or grand master keys), performing regular audits helps your peace of mind knowing that you aren’t missing master keys and that high-level access is limited to those who need it. If your key holders can’t account for all keys, rekeying affected locks is recommended. Key audits are an ideal time to brush up on key control policy with key holders, as well.
Key Tracking Software
![]()
Tracking keys across your organization can be a hassle or a breeze depending on how you’re doing it. While a paper trail or spreadsheet can work for smaller organizations with fewer keys to track, larger organizations with many key holders and levels of access need more comprehensive key tracking ability. The best way to track your keys is with cloud-based tracking software.
Cloud-based software provides continually up-to-date information and visibility into the performance of your key system and can be used by multiple stakeholders, unlike standalone key tracking software that is downloaded to a single computer. We developed modernized, cloud-based key control software to give you comprehensive insight into your key management, including key tracking, lock changes, and other record modifications.
Learn more about how to make tracking any brand of keys in any key system structure (master or not) faster and more efficient with our free ebook: